Method 1. Repair Bootloader
To repair Bootloader, you should prepare a Windows 10 installation disc.
Step 1. Boot from Windows 10 installation disc and press any key to continue.
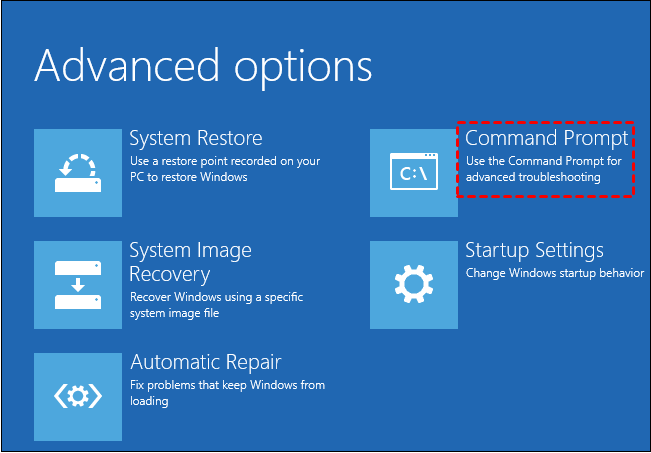
Step 2. Then navigate to Repair your computer->Troubleshoot->Advanced options->Command Prompt.
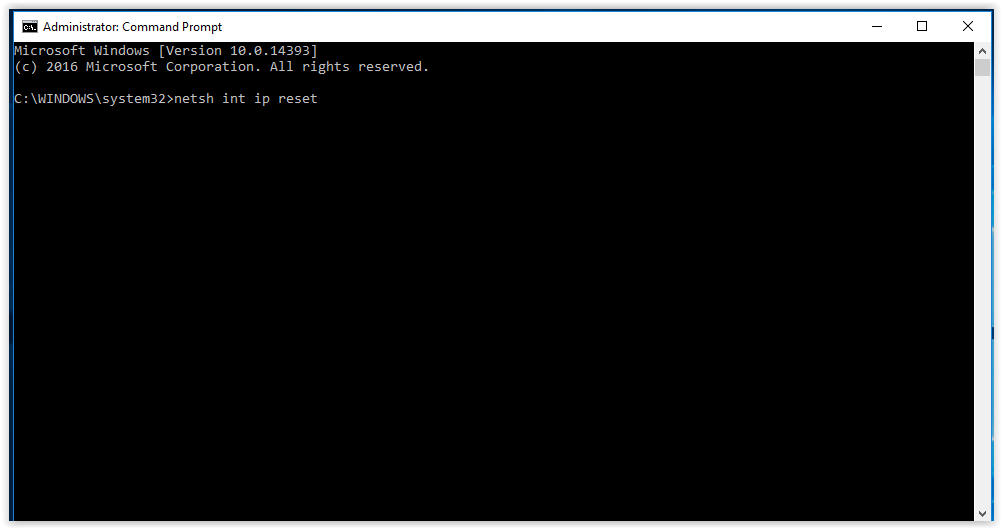
Step 3. Type diskpart in the command prompt.
Step 4. Type the following command and press Enter after each command.
•list disk
•sel disk 0 (where 0 stands for the boot drive)
•list vol (note which volume is the EFI partition, mine is 4)
•sel vol 4
•assign letter=N:
•exit
Step 5. Type N: (the drive letter you just assigned and hit Enter.)
Step 6. After you have assigned a drive letter Using Diskpart, you can format the EFI partition using the following command.
•format N: /FS:FAT32
Step 7. Now, type bcdboot C:\windows /s N: /f UEFI and hit Enter. This command will repair your Bootloader.
Then try the bootrec /fixboot command again, fixboot access denied in Windows 10 could be solved.